Question 14:
A security analyst is reviewing packet captures from a system that was compromised. The system was already isolated from the network, but it did have network access for a few hours after being compromised. When viewing the capture in a packet analyzer, the analyst sees the following:
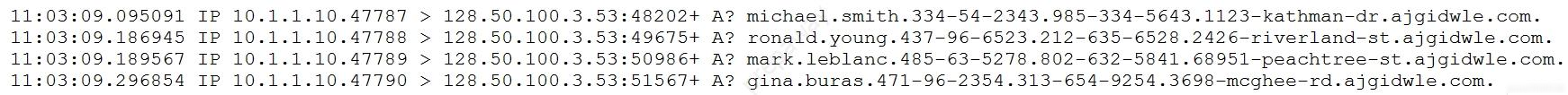
Which of the following can the analyst conclude?
Answer options:
A. Malware is attempting to beacon to 128.50.100.3. B. The system is running a DoS attack against ajgidwle.com. C. The system is scanning ajgidwle.com for PII. D. Data is being exfiltrated over DNS.