Question 29:
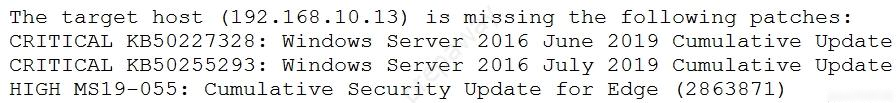
A security analyst is evaluating two vulnerability management tools for possible use in an organization. The analyst set up each of the tools according to the respective vendor`s instructions and generated a report of vulnerabilities that ran against the same target server. Tool A reported the following:
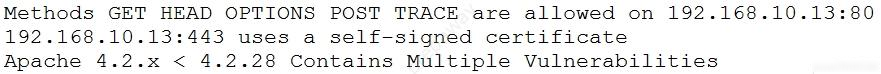
Tool B reported the following:
Which of the following BEST describes the method used by each tool? (Choose two.)
Answer options:
A. Tool A is agent based. B. Tool A used fuzzing logic to test vulnerabilities. C. Tool A is unauthenticated. D. Tool B utilized machine learning technology. E. Tool B is agent based. F. Tool B is unauthenticated.