Question 154:
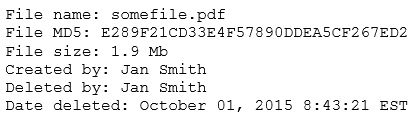
A security analyst reviews the following output:
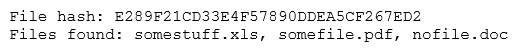
The analyst loads the hash into the SIEM to discover if this hash is seen in other parts of the network. After inspecting a large number of files, the security analyst reports the following:
Which of the following is the MOST likely cause of the hash being found in other areas?
Answer options:
A. Jan Smith is an insider threat B. There are MD5 hash collisions C. The file is encrypted D. Shadow copies are present