Question 84:
An information security specialist is reviewing the following output from a Linux server.
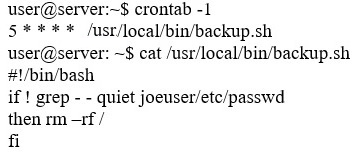
Based on the above information, which of the following types of malware was installed on the server?
Answer options:
A. Logic bomb B. Trojan C. Backdoor D. Ransomware E. Rootkit